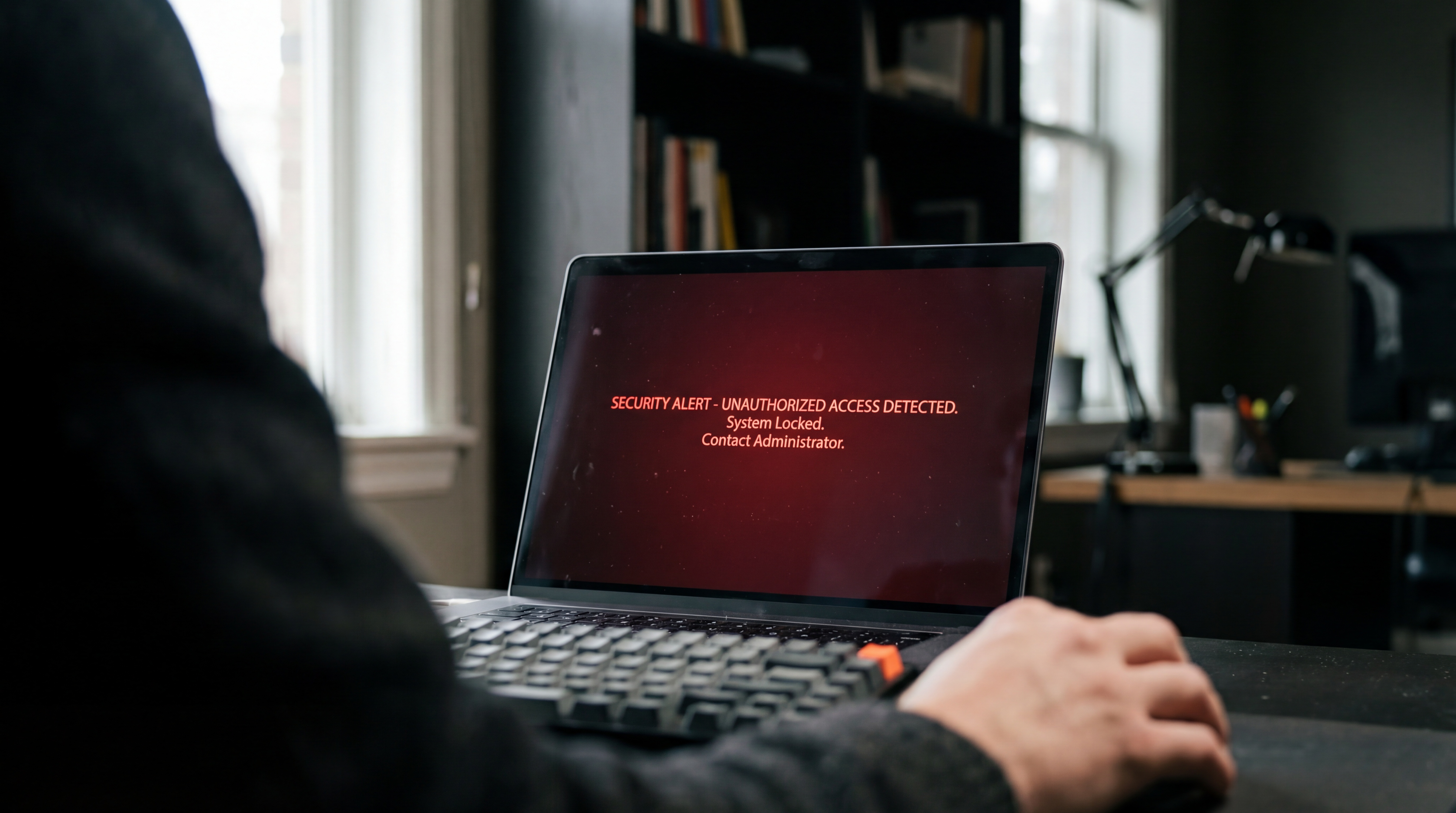
Telnyx, a popular communication platform, has fallen victim to a security breach on PyPI, the Python Package Index. A compromised package under the Telnyx name was uploaded, potentially exposing developers to malicious code. This incident raises urgent concerns for AI practitioners and developers relying on PyPI for their project dependencies.
This article was inspired by "Telnyx package compromised on PyPI" from Hacker News.
Read the original source.
Scope of the Compromise
The compromised Telnyx package was detected on PyPI, a repository hosting over 400,000 packages used by millions of developers. While specific details on the payload remain limited, early reports suggest the package could execute unauthorized code, risking data theft or system hijacking. The breach was flagged through community vigilance, underscoring PyPI’s ongoing struggle with supply chain attacks.
Bottom line: A single compromised package can jeopardize entire projects, highlighting the fragility of open-source ecosystems.
Community Reaction on Hacker News
The Hacker News discussion garnered 83 points and 1 comment, reflecting significant concern among developers. Key feedback includes:
- Alarm over the ease of uploading malicious packages to PyPI.
- Calls for stricter verification processes for package maintainers.
- Urgency for developers to audit dependencies in their AI and ML projects.
The limited comment count suggests the story is still unfolding, but the high point score indicates broad interest in supply chain security.
Why This Matters for AI Developers
AI projects often rely on extensive libraries from PyPI for model training, data processing, and deployment. A compromised package like Telnyx could infiltrate pipelines, exposing sensitive data or skewing model outputs. With over 60% of developers reusing code without thorough vetting (per recent surveys), this breach is a wake-up call for tighter security practices.
How to Protect Your Projects
Mitigating risks from such breaches requires immediate action. Developers should:
- Verify package authenticity by cross-checking with official sources like Telnyx’s GitHub.
- Use tools like
pip-auditto scan for known vulnerabilities in dependencies. - Limit installations to trusted versions with verified checksums.
Bottom line: Proactive dependency management is no longer optional—it’s critical for secure AI development.
"Technical Context on PyPI Attacks"
PyPI attacks often exploit typosquatting (mimicking legitimate package names) or compromised maintainer accounts. Malicious packages can execute code during installation, accessing local files or network resources. Recent stats show over 200 malicious packages removed from PyPI in 2023 alone, per security reports.
The Bigger Picture
This Telnyx incident is part of a growing trend of supply chain attacks targeting open-source repositories. As AI and ML workflows become more dependent on external libraries, the attack surface expands. Developers and organizations must prioritize security hygiene to prevent such breaches from derailing innovation in the AI space.



Top comments (0)